How To Cut EMS Patient Collection Time With Digital-first Billing and Payment
ZOLL Online – High Performance In A Secure Environment
We understand it’s not easy for an organization to give up some control of their systems and processes, especially when it comes to data and system security

We understand it’s not easy for an organization to give up some control of their systems and processes, especially when it comes to data and system security. That’s why at ZOLL, we’ve taken every precaution to build ZOLL Online from the ground up with system architecture, security and performance best practices in mind. This attentetion to detail should help you sleep well knowing that your data is secure 24 hours per day, 7 days per week. Here is an outline of some of the measures we’ve taken to ensure your data is safe and secure and your software is performing well.
ZOLL Online System Architecture & Security Environment
Physical Security. The physical security of ZOLL’s hosting infrastructure encompasses 24x7 security staff, badge access, and video security throughout the facility managed to PCI DSS, HIPAA and SAS70 type II compliance standards. ZOLL stores your information in our world-class data center where SunGard employs 24/7/365 video surveillance, strict personnel access controls, mantraps, on-site security, and third party audits to keep your information safe. Any visitor to the data center must be authorized, and further authorization is required to access areas with servers, workstations, or networking equipment.
Network Security. Security and segregation of virtual environments within SunGard’s Enterprise Cloud Service is provided using VCE Vblock technology and best practices provided by the VCE consortium. Specifically, Sungard uses firewalls and VLAN’s for network separation at layer 3, physical LUNS for storage separation at the hardware abstraction layer, Vsphere for secure separation at the hypervisor layer, and IDS/IPS monitoring and reporting on the infrastructure. ZOLL Online applications operate on a private, secure, and completely separate network from other networks within the data center. Low-level logical separation ensures that your data cannot be leaked between networks, even in the event of a programming error. Access to both the software and its underlying infrastructure systems is logged.
Security Validated Internally & by Third-Party Auditors. Internal self-audits are performed by ZOLL which include weekly external network vulnerability scans as well as verification of user access controls. Self-audits are also performed ad-hoc when significant network or system changes occur. ZOLL also engages with certified 3rd party auditors who run annual penetration tests and also verify internal security policies and practices.
World Class Hosting Facility
Data Center Overview. SunGard provides a tier 3 level datacenter with state of the art security and technological facilities located in Philadelphia and Aurora, Colorado. They provide expert level systems and software support as a supplemental resource to the internal ZOLL datacenter engineering team.
Physical Plant
-
150,000 square foot single tenant building constructed in 2001
-
34,500 sq. ft. of 30” raised floor
Power Management
-
11 MW rated utility feed from high availability substation
-
(5) 2 MW Cummins generators with 34,000 gallon fuel tank onsite
-
(12) 750 kVA UPS modules (2N redundancy)
Environmental Control and Safety
-
(2) 520 ton chillers with (2) 600 ton cooling towers (N+1 redundancy)
-
(12) 26 ton CRAC units
-
VESDA (Very Early Smoke Detection Apparatus) fire detection systems
-
FE227 fire suppression systems
-
Fire station adjacent to property
Issue Resolution and Data Protection
The ZOLL datacenter team and SunGard’s datacenter support staff both actively monitor the systems at the datacenter. Hardware related issues are addressed by SunGard’s expert hardware staff. Proactive monitoring using tools such as PRTG and Nagios allows both the ZOLL and SunGard teams to expeditiously address issues to prevent or minimize outages. In the event of an issue of any kind, both SunGard and ZOLL’s datacenter team are alerted and respond immediately. In the event of a catastrophic database server hardware or operating system failure, the standby database server will be brought online.
High Availability Design
Hosting Platform Resiliency. SunGard’s implementation of Vblock (VSphere, UCS, Clariion, and NEXUS) and accompanying configuration of the orchestration layer delivers a 99.95% availability SLA (per VM per month) without the need or cost of traditional, hardware-intensive and highly expensive hardware and software clusters. Host level failure resolution utilizes the HA feature of VMware to restart the failed VM on another blade within a matter of minutes.
ZOLL has equipped its data center with load balancers and redundant core switches to ensure the integrity and availability of your data. Customer data is automatically backed up. Issues that may occur with the system are addressed in tandem by both ZOLL engineers and SunGard support staff.
Internet Redundancy. SunGard uses multiple internet providers with multiple feeds from each:
(4) Tier 1 Internet providers with direct connections to their backbone networks
-
(2) Sprint OC 48 connections
-
(4) Qwest OC 48 connections
-
(2) Level3 OC 48 connections
-
(2) Verizon OC 48 connections
(2) Juniper core switches with multicarrier meshed connections to backbones outlined above
(6) Cisco 6500 series core switches
Application & Server Design
Application Security Features. Connections to ZOLL Online applications are done over the internet using a secure channel (SSL 3.0/TLS), ensuring that the transmission of data between your computer and ZOLL is never compromised. ZOLL Online does not store plain text passwords. Instead passwords are converted to salted hashes and stored as such. Passwords must be 8 characters in length, require mixed-case as well as 1 number or special character. Passwords are required to be changed every 90 days and time services are utilized to guarantee all systems are in sync with the same date and time.
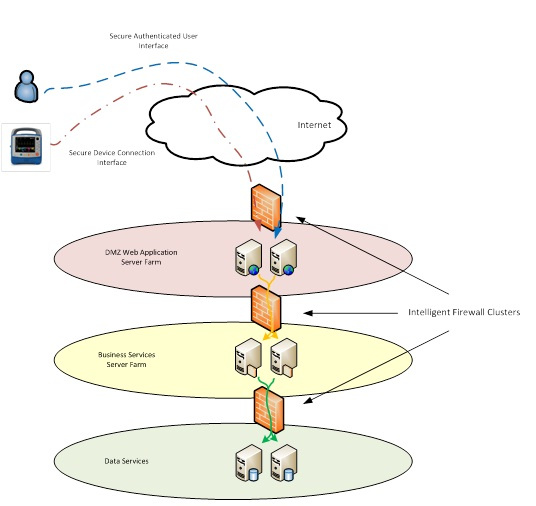
Server Architecture. Windows 2008 R2 ASP .Net IIS7 web servers are deployed in redundant farms for scalability and high availability. The web server farm resides in a perimeter DMZ, while database servers are segregated by a firewall to limit access and safeguard information. All servers are virtualized to leverage the HA features of the Vblock architecture. ZOLL deploys anti-virus software across systems to protect against newly discovered threats and malware. ZOLL Online is a multi-tenant infrastructure; direct server access, monitoring systems access as well as direct access to data is disallowed to all ZOLL clients to protect their privacy. All ZOLL Online systems are internally developed and do not rely on external third party cloud services.
Authentication, Authorization & User Roles. All users are required to log in using their username and password. Users can be assigned the “administrator” role. These users will assign rights to other users using other roles which will determine what the user is authorized to access. Upon creating an account, users are presented with a system generated password. Users are required to change their original temporary password and can change their password at will. Users may not use one of their past five passwords. Passwords expire after ninety days. The users who have the “administrator” roll can manage users and passwords and perform other general account management tasks. User actions are logged including create, read, update, and delete.
Logical Data Flow. Users and devices connect to the ZOLL Online systems’ presentation layer through the application-aware firewall:
Client Requirements. ZOLL online is a SaaS based application which does not require the user to have local administrative access to their computer. ZOLL Online applications are browser based and generally run without requiring the installation of an additional local client application. For normal use cases, no services or applications need to be added to the client computers.
Capacity Planning. ZOLL has leveraged the flexibility of virtualization to build a highly scalable infrastructure that allows server farms to grow with increased load. Load balancing technology enables ZOLL to add new virtual servers with minimal or no customer impact.
Database Design
Database Security Features. All data is protected in the database which is secured behind multiple layers of firewalls, user presentation layers, and business service layers all of which require authentication maintained and set by the system itself. Additionally all users accessing the user presentation layer must authenticate to the system before they can access data over SSL encryption.
Database Backups. All databases are backed up regularly. Full backups are done daily and hourly backups are done throughout the day. Database redundancy is also used to protect against hardware or operating system failure.
HIPAA & HITECH Compliance
Regulatory Compliance. HIPAA Business Associate Agreements are maintained between ZOLL and service providers. Annual risk assessments are conducted by a security auditor to validate that ZOLL is maintaining appropriate data controls. SunGard’s facility and services are also audited regularly and adhere to the same level of standards and more. Additional information regarding audits is available upon request. In the unlikely event of a security breach, ZOLL will utilize forensic systems to determine the scope of the breach and notify affected customers immediately.
ZOLL Datacenter IT Staff
ZOLL Data Center Team. The ZOLL data center team is composed of experienced IT personnel whom have many years of experience in both IT system design and architecture as well as system security. ZOLL verifies the integrity of its team members prior to their joining the team by performing background checks as well as industry reference verification. The team uses industry proven best practices throughout the design and management of the ZOLL Online environment.
ZOLL Software Development Team. The software development team at ZOLL is well versed in and uses Agile Development methodologies to ensure product development is always moving forward and enhancing the products. Also, the team is constantly improving design to provide both the best possible online experience as well as maintaining system and data integrity. The team is composed of highly skilled and experienced software developers and quality assurance engineers and adheres to various policies and protocols to protect the customer such as utilizing software escrow and strictly following a stringent software release process.
Click here to view the latest ZOLL Online System Architecture & Security information and to download the latest document.
Related Posts
How EMS Agencies Can Use Technology To Drive Timely Patient Payments
Doing More With Less: How Dispatch Automation Benefits EMS Operations
ZOLL Pulse Blog
Subscribe to our blog and receive quality content that makes your job as an EMS & fire, hospital, or AR professional easier.
ZOLL Pulse Blog
Subscribe to our blog and receive quality content that makes your job as an EMS, fire, hospital, or AR professional easier.